Quantum Key Distribution Scheme
Charles Bennett’s Quantum Key Distribution (BB84) and the Role of Non-Commuting Observables
The BB84 protocol (Bennett–Brassard, 1984) enables two parties, Alice and Bob, to establish a shared random secret key over an insecure quantum channel. Security arises from fundamental quantum principles: superposition, the no-cloning theorem, and—crucially—the incompatibility of measurements in non-commuting bases.
1) Two Non-Commuting Measurement Bases
Rectilinear (Z) basis, associated with the Pauli operator ![]() :
:
![]()
Diagonal (X) basis, associated with the Pauli operator ![]() :
:
![]()
These bases are incompatible because their observables do not commute:
![]()
Operationally: measuring a qubit prepared in one basis using the other basis yields random outcomes and irreversibly disturbs the state.
2) BB84 Protocol Steps
- Preparation (Alice): For each bit, Alice chooses a random basis (
 or
or  ) and prepares one of the four states
) and prepares one of the four states 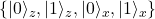 . She sends the photon to Bob.
. She sends the photon to Bob. - Measurement (Bob): For each photon, Bob randomly chooses to measure in
 or
or  and records the result.
and records the result. - Basis reconciliation (public channel): Alice and Bob announce which basis they used (not the bit values). They keep only positions where their bases match—this forms the raw key.
- Error estimation & post-processing: They sacrifice a random subset of raw bits to estimate the error rate. If below threshold, they run classical error correction and privacy amplification to obtain the final shared secret key.
3) How Non-Commuting Observables Enforce Security
Suppose an eavesdropper, Eve, intercepts and measures each photon:
- If Eve picks the correct basis (matches Alice’s), she learns the bit without disturbance.
- If Eve picks the wrong basis, non-commutativity implies her measurement outcome is random, and the post-measurement state collapses into the wrong basis. When Bob later measures (possibly in the correct basis), errors are introduced.
For example, if Alice prepares ![]() but Eve measures in the
but Eve measures in the ![]() basis, Eve’s outcome is uniformly random:
basis, Eve’s outcome is uniformly random:
![]()
Eve then forwards her collapsed state to Bob. If Bob measures in the ![]() basis, his result is also random given Eve chose the wrong basis:
basis, his result is also random given Eve chose the wrong basis:
![]()
Since Eve guesses the correct basis with probability ![]() and flips the bit with probability
and flips the bit with probability ![]() when she is wrong, a simple intercept-resend attack produces an average quantum bit-error rate (QBER) of about
when she is wrong, a simple intercept-resend attack produces an average quantum bit-error rate (QBER) of about ![]() in the sifted key—a level Alice and Bob can detect during error estimation.
in the sifted key—a level Alice and Bob can detect during error estimation.
The underlying reason is formal:
![]()
so one cannot jointly measure ![]() and
and ![]() with arbitrary precision. This is the measurement-incompatibility (Heisenberg-type) constraint that makes undetected eavesdropping impossible in ideal conditions.
with arbitrary precision. This is the measurement-incompatibility (Heisenberg-type) constraint that makes undetected eavesdropping impossible in ideal conditions.
4) Key Insight & Comparison
Security in BB84 is physical, not computational. It derives from quantum mechanics—superposition, no-cloning, and especially non-commuting observables—rather than hardness assumptions (like factoring).
| Component | Classical Crypto | Bennett’s QKD (BB84) |
|---|---|---|
| Security Basis | Computational hardness (e.g., factoring) | Quantum physics (non-commuting measurements, no-cloning) |
| Eavesdrop Detection | Not intrinsic | Intrinsic — measurement introduces errors |
| Key Distribution | Secure classical channel required | Quantum channel + authenticated classical channel |
5) Minimal Math Recap
Basis change between ![]() and
and ![]() (Hadamard rotation):
(Hadamard rotation):
![]()
Non-commutation:
![]()
Wrong-basis measurement randomness:
![]()